Administrator
Handbook
www.loriotpro.com
Administrator
Handbook |
TOC |
When using OID in the request/response packet the last values should specify the instance of the object. Instance is particularly useful to select a element among a group of similar element. This is the case when using network switches. Switches are made of a chassis containing multiple boards, sometimes daughter boards, each of them having ports.
Example : the following OID is used to get the number of incoming octets on the port 3 located on the daughter board 2 of the board 2 of this device switch.
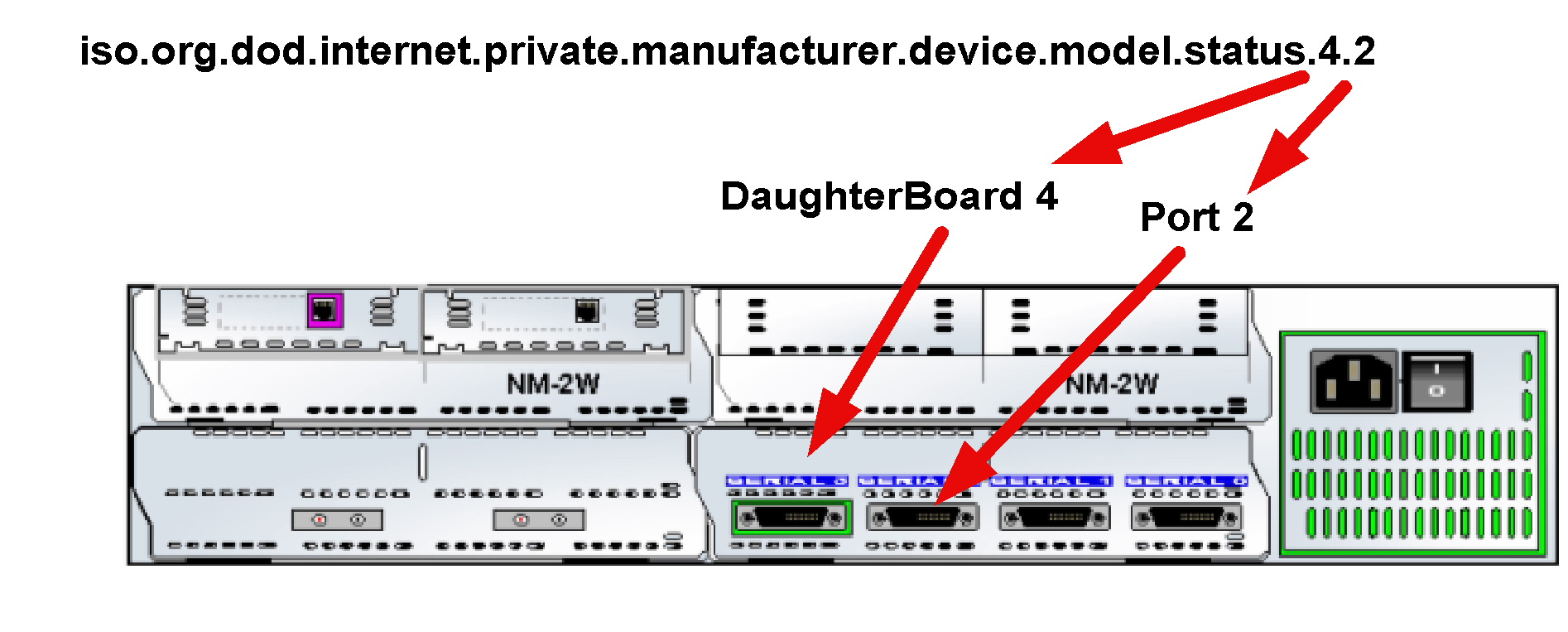
The zero value points the object itself (here the chassis) and is the default one.
Event management (TRAPs)Agent has the ability of sending packets on his own called TRAPs. The initial configuration of the agent specify an IP address where to send it, normally the management station run a trap receiver process.
About TRAPs and LoriotPro:
Loriot Pro manages SNMP V1 traps and notifications of informs from SNMP v2c and v3 (subset only). Traps are displayed in the windows trap manager. Filters allow the administrator to select the traps to display and to trigger and action.
Security and communityThe security is become an unavoidable constrain in the contemporary information system. The initial security mechanisms designed in SNMP version 1 are now not enough secured to protect effectively access to devices. SNMP V2 and especially V3 added strong authentication between agents and the manager.
SNMP defines a kind of password protection by the concept of Communities. A community is given to a group of devices under the control of an authorized administrator. Without the community it is impossible to make SNMP request to devices.
Meanwhile it is impossible to affect rights to identified administrators and have access granularity on managed objects.
There are three communities in SNMP v1 and V2c. Communities are set up when configuring the device
A manager should know the devices communities of a device to read or write objects. The lack of security comes from the fact that the password is sent in clear text in SNMP packets on the network and a hacker could easily capture it.
Another common level of protection is to specify in the agent configuration the IP address of the manager that could send SNMP request. However, this address is easy to mystify.
The version 3 of SNMP allows multiple methods of protection against hacking based on identification, strong authentication and encryption.
LoriotPro supports authentication with a named profile and a password, using the algorithm HMAC-MD5-96.
The SMI - Structure of Management Information specify the rules that should be followed when creating objects in MIB files. It is a subset of ASN1 – Abstract Syntax Notation from the OSI model. The objects are defined in a hierarchical tree structure. This global naming tree ensures that all object names are unique and gives a unique way for finding them.
The RFC1155 defines the rules to apply in version 1. The version 2 of the SMI is also available and MIB files could use either the SMI v1 or the SMI v2.
The following graph shows a part of the SMI tree:
а 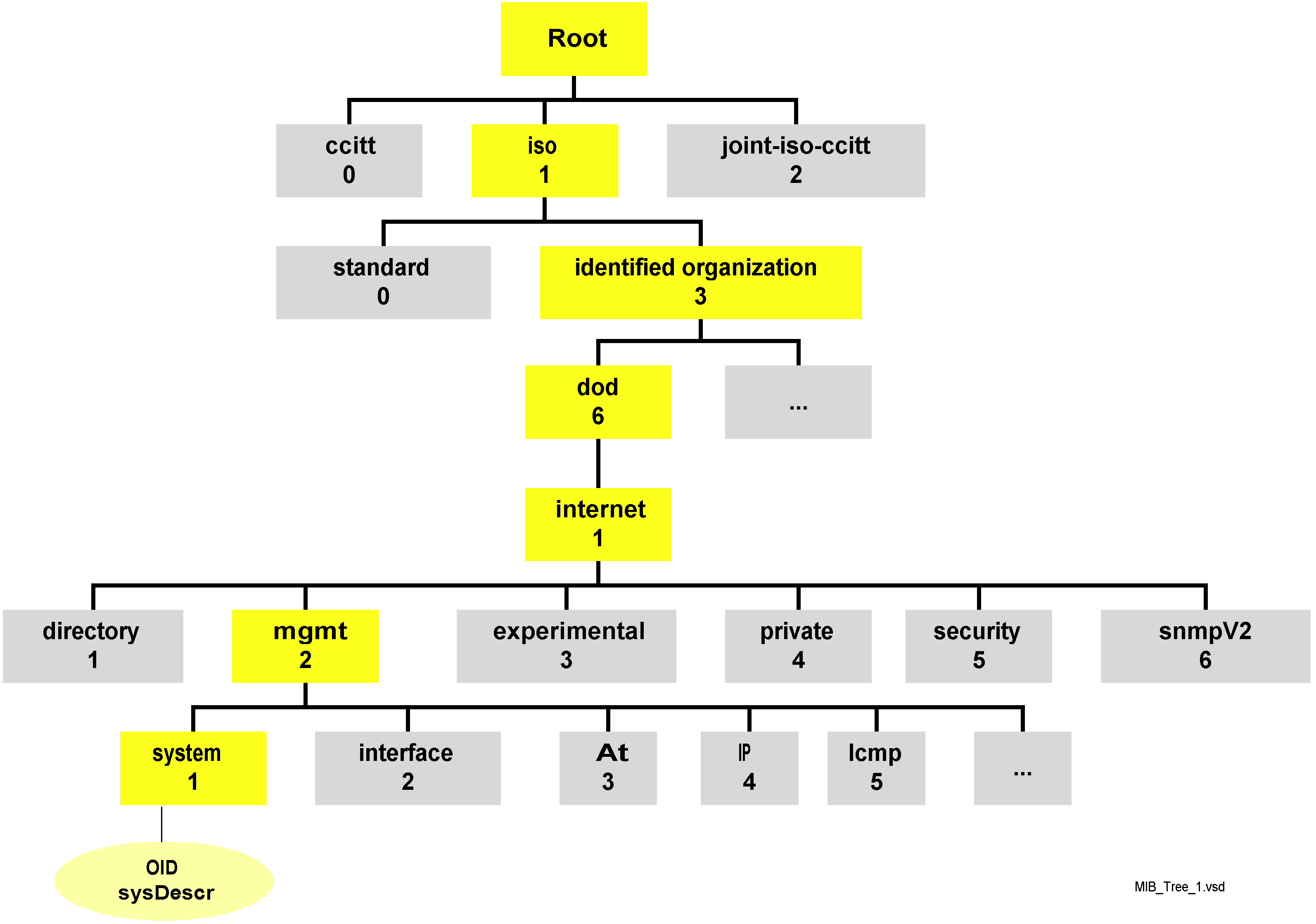
Tree structure of SNMP objects
Each object is identified by is OID (Object Identifier). L’OID has two display formats (nominal and numeric). In PDU the numeric format is used by the protocol. Programs use the nominal format, easier to manipulate by human brain. The SNMP manager established the relation through the compiled MIB.
Example
| Nominal |
iso.org.dod.internet.mgmt.mib-2.ip.ipInReceives |
| Numeric |
1.3.6.1.2.1.4.3 |
Here after the SMI v1 structure defining the top objects in the tree.
а-- аRFC1155 MIB
RFC1155-SMI DEFINITIONS ::= BEGIN
-- the path to the root
orgаааааааааа аааааааааааа OBJECT IDENTIFIER ::=
{ iso 3 }
dodааааааааа ааааааааааааа OBJECT IDENTIFIER ::=
{ org 6 }
internetаааа аааааааааааа OBJECT IDENTIFIER ::=
{ dod 1 }
directoryаааа аааааааааа OBJECT IDENTIFIER ::= {
internet 1 }
mgmtааааааааа ааааааааа OBJECT IDENTIFIER ::= {
internet 2 }
experimentalа OBJECT IDENTIFIER ::= { internet 3 }
privateаааааа ааааааааааа OBJECT IDENTIFIER ::=
{ internet 4 }
enterprisesа аааааааа OBJECT IDENTIFIER ::= { privateа
1 }
mib-2аааааааа аааааааааа OBJECT IDENTIFIER ::= {
mgmt 1 }
END
The SMI V2 notation is quite different from v1 in the construction of the logical structure of MIB files and of the global naming tree. The RFC 1902 describes these enhancements.
--ааааааааааа RFC 1902
SNMPv2-SMI DEFINITIONS ::= BEGIN
-- the path to the root
orgааааааааааа ааааааааааа OBJECT IDENTIFIER ::=
{ iso 3 }
dodааааааааааа ааааааааааа OBJECT IDENTIFIER ::=
{ org 6 }
internetаааааа аааааааааа OBJECT IDENTIFIER ::=
{ dod 1 }
directoryааааа ааааааааа OBJECT IDENTIFIER ::= {
internet 1 }
mgmtаааааааааа аааааааа OBJECT IDENTIFIER ::= {
internet 2 }
mib-2ааааааааа ааааааааа OBJECT IDENTIFIER ::= {
mgmt 1 }
transmissionаа ааааа OBJECT IDENTIFIER ::= { mib-2
10 }
experimentalаа ааааа OBJECT IDENTIFIER ::= { internet
3 }
privateааааааа аааааааааа OBJECT IDENTIFIER ::=
{ internet 4 }
enterprisesааа OBJECT IDENTIFIER ::= { private 1 }
securityаааааа ааааааааа OBJECT IDENTIFIER ::= {
internet 5 }
snmpV2ааааааа ааааааа OBJECT IDENTIFIER ::= { internet
6 }
-- transport domains
snmpDomainsааа а OBJECT IDENTIFIER ::= { snmpV2
1 }
-- transport proxies
snmpProxysаааа ааа OBJECT IDENTIFIER ::= { snmpV2
2 }
-- module identities
snmpModulesааа аа OBJECT IDENTIFIER ::= { snmpV2
3 }
-- definitions for information modules
END
The first sublevel under root is the iso object followed by the org object and so on. Each object has a number in the tree.
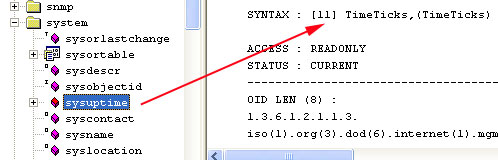
Here is an example for the object “sysname” and how you can see it with the LoriotPro MIB browser
The nominal format:
аiso(1).org(3).dod(6).internet(1).mgmt(2).mib-2(1).system(1).sysname(5).0.
or the numerical format : 1.3.6.1.2.1.1.5.0
Object typesObjects are from different types.
Scalar. A scalar object can be assigned values without structures
Table. Table objects are structured arrays and could be indexed.
The following unstructured data types could also be used :
Counter: A non-negative Integer that is incremented until it reaches a maximum value. When the maximum value is reached the counter wrapper (reset to 0)
Gauge: A non-negative Integer that could oscillate between 0 and a maximum value.
IpAddress: A 32 bits address in dotted octet format (Example: F1:01:45:56)
NetworkAddress: Used to store network address.
Opaque: Used to encapsulate non-formatted data
TimeTicks: A non-negative integer used to keep track of time in 100th of seconds.
Examples of object
Example of table object:
| sysDescr |
Describe the model and the mark of the equipment. |
| IfEntry |
This object contains a synthesis table of equipment’s network interfaces. |
| ipRouteTable |
This object contains the IP routing table of the host. |
The following text is an extract of the MIB file and describes the table object AtEntry :
ааааааааа AtEntry ::=
ааааааааааааа SEQUENCE {
ааааааааааааааааа atIfIndex
ааааааааааааааааааааа INTEGER,
ааааааааааа ааааааatPhysAddress
ааааааааааааааааааааа PhysAddress,
ааааааааааааааааа atNetAddress
ааааааааааааааааааааа NetworkAddress
ааааааааааааа }
Example of scalar :
We use the the ‘MIB Query’ tool from LoriotPro to query the scalar object sysDescrа from 10.33.10.121 agent, its current value is displayed in the Result window. This is string type data.

Query on 10.33.10.121 agent for its sysdescr objet
Example of table query :
The ifentry object displayed hereafter on its table format contains a set of scalar objects.
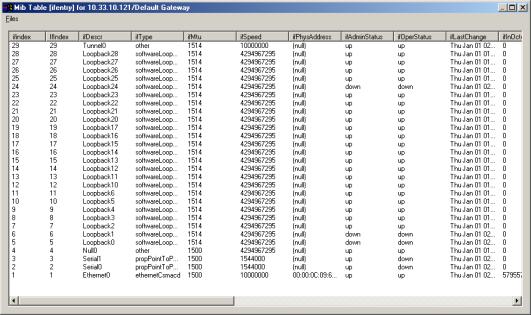
Query on 10.33.10.121 agent for ifentry table
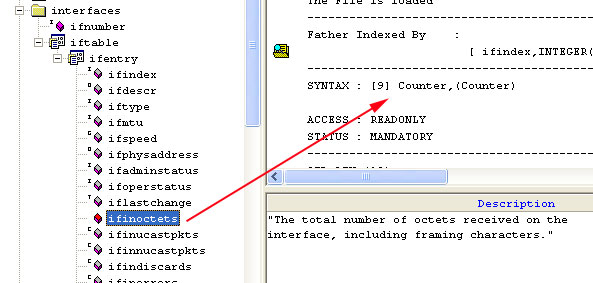
Example of object of Counter type viewed from the LoriotPro Wizard
Example of object of Gauge type from the LoriotPro Wizard

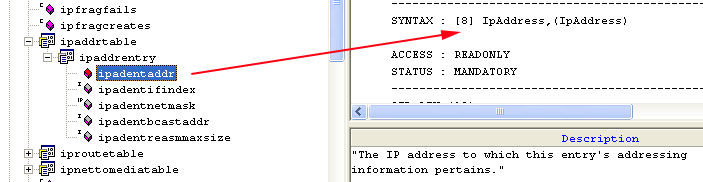
Example of object of IP address entry type from the LoriotPro Wizard
Example of object of TimeTicks type from the LoriotPro Wizard